There are a few built-in troubleshooting utilities that can help diagnose slow Ubuntu boot issues.
Via the terminal enter the cmd:
systemd-analyze
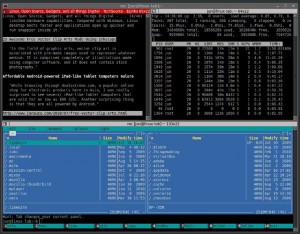
An output like the following is displayed
Startup finished in 4.901s (firmware) + 4.113s (loader) + 16.613s (kernel) + 13.768s (userspace) = 39.397s
To find out key processes, type:
systemd-analyze blame
A list of applications/services is displayed with the longest consuming (time) at the top. Example:
7.737s NetworkManager-wait-online.service
2.837s dev-mapper-Ubuntu\x2drootvol.device
2.313s lvm2-monitor.service
1.780s systemd-tmpfiles-setup-dev.service
1.708s systemd-sysctl.service
1.120s vmware-workstation-server.service
704ms ModemManager.service
658ms accounts-daemon.service
610ms lightdm.service
To view a graphical version of this data, enter:
systemd-analyze plot > output.html
This creates a HTML file that includes a graphic showing the boot time, along with the acivities, duration etc.
Typing:
systemd-analyze critical-chain
Provides a command-line output ( a simple version) of the processes), like the following:
The time after the unit is active or started is printed after the “@” character.
The time the unit takes to start is printed after the “+” character.
graphical.target @13.765s
└─multi-user.target @13.765s
└─vmware-workstation-server.service @12.644s +1.120s
└─network-online.target @12.046s
└─NetworkManager-wait-online.service @4.308s +7.737s
└─NetworkManager.service @3.731s +575ms
└─dbus.service @3.686s
└─basic.target @3.680s
└─sockets.target @3.680s
└─clamav-daemon.socket @3.678s +777us
└─sysinit.target @3.675s
└─apparmor.service @3.471s +203ms
└─local-fs.target @3.470s
└─run-vmblock\x2dfuse.mount @12.637s
└─local-fs-pre.target @2.726s
└─lvm2-monitor.service @412ms +2.313s
└─lvm2-lvmetad.service @583ms
└─system.slice @398ms
└─-.slice @370ms
Great utilities for identifying bottle necks and slow boot up performance.