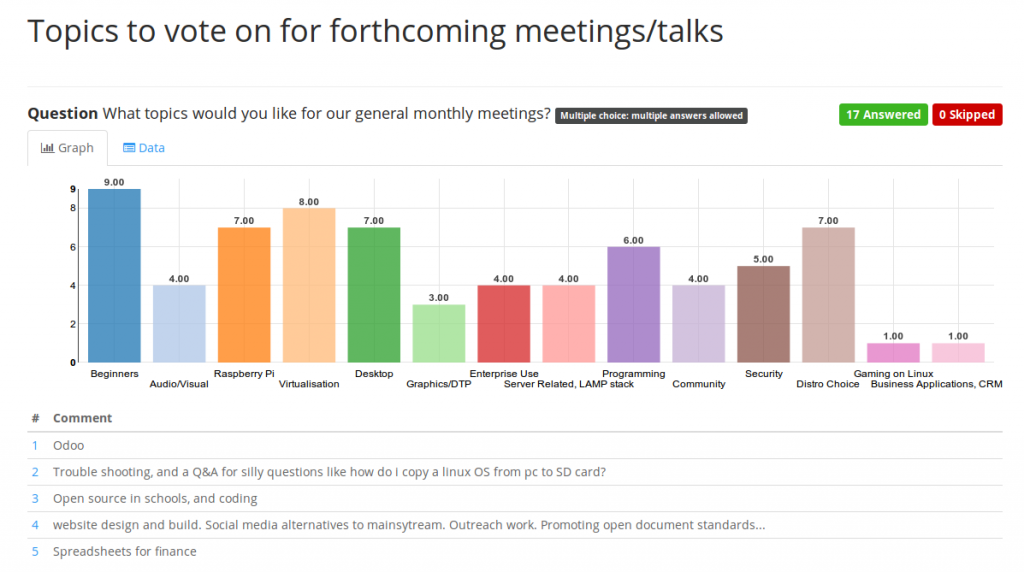
You will see that there is quite an interest in Beginners topics, choice of Distro, interest in Virtualisation, Desktop and Raspberry Pi, and Programming. Topics such as Gaming on Linux, Business applications, such as CRM/ERP and Graphics faired less well. There were a few extra topics requested which you can also see listed, such as a Troubleshooting session (sounds a good one), outreach and spreadsheets for finance.
As discussed at the last LUG Meeting we plan the first meeting based around these topics in June 24th, 4th Wednesday of the month as usual, probably to allow time to get organised. What seemed like a good plan at the meeting is to have a Beginners session that also includes Distro choice, ie why I should choose Ubuntu over Debian, Fedora or Arch for example.
In the end we had 17 responses altogether not too bad, although people were allowed to vote for as many topics as they wanted which seemed like the fairest method to use.
I will setup a Pirate pad (or equivalent) online pad where we can share our plans for this first meeting. There wasn’t consensus where we should hire a room and and have a full session, or just keep things simple and carry on at the Courtyard but please say your ideas on this .
We will also need people who are happy to talk about topics for Beginners, and structure the event. I’m happy to help coordinate, but it’s always best to get as many volunteers to help to reduce the load for the others.
We will also of course need to plan what other events for each month we will hold based around the interest shown above.
So please reply and let everyone know your thoughts, plans and ideas and/or if you want to help
 http://torios.net/
http://torios.net/
